Code Security Intelligence
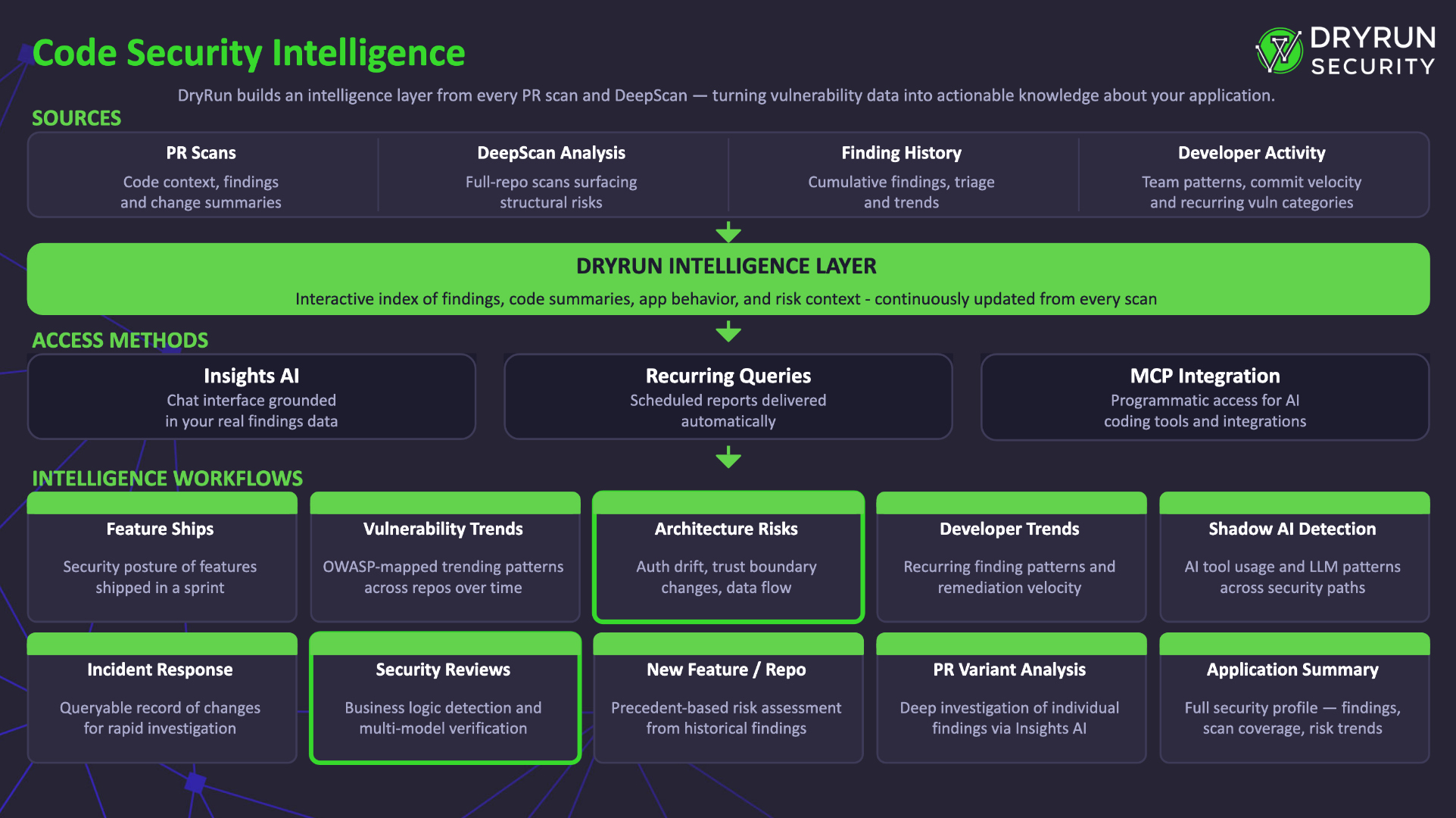
DryRun Security builds an intelligence layer on top of vulnerability findings and scan data, enabling actionable security workflows across your codebase and development organization.
Overview
DryRun Security takes vulnerability scanning to the next level by building an intelligence layer on top of all the finding data and trends from PR scanning and DeepScan. This intelligence layer is actionable and enables AppSec teams to do meaningful security work beyond just reviewing individual findings, surfacing trends, patterns, risks, and insights across the entire codebase and development organization.
Every pull request DryRun Security reviews and every DeepScan contributes to a structured, queryable intelligence index. This index powers a range of security workflows that would otherwise require manual data collection, spreadsheet tracking, and cross-referencing multiple tools.
Intelligence Workflows
The intelligence layer enables a range of security workflows. Each workflow draws on the findings and scan data DryRun Security continuously collects across your repositories.
| Workflow | What It Shows | Example Use Case |
|---|---|---|
| Feature Ships | Security posture of features shipped in a sprint or release, with risk annotations and PR links | Summarize the security status of features shipped this sprint for a release review |
| Vulnerability Trends | Trending vulnerability patterns and coverage data across repos over time, including OWASP Top 10 mapping | Compare critical finding counts quarter over quarter to measure security program effectiveness |
| Architecture Risks | Structural risk patterns in the codebase, including trust boundary changes, auth drift, and data flow modifications | Identify new unauthenticated endpoints or service-to-service communication paths added this month |
| Developer Trends | Which teams or repos have recurring finding patterns, remediation velocity, and code change activity | Determine which teams would benefit most from targeted security training based on finding patterns |
| Shadow AI | AI and LLM usage detected across the codebase: tool fingerprints, code pattern analysis, and volume anomalies | Audit all AI-generated code contributions in security-critical paths for governance reporting |
| Incident Response | Queryable record of code changes, findings, and triage decisions for rapid incident investigation | Trace which PR introduced a vulnerable dependency and assess blast radius during an active incident |
| Application Summary | Security profile of a specific service or application: open findings, scan coverage, and risk trends | Generate an application security profile for a new team member onboarding onto a service |
| Security Reviews | Contextual security analysis results, business logic detection, and multi-model verification insights | Investigate which findings required cross-file analysis to detect and would be missed by pattern matchers |
| New Feature/Repo Review | Precedent-based risk assessment for new features or repositories using historical findings | Before building a new payment integration, review security findings from similar past implementations |
| PR Variant Analysis | Deep investigation of individual PR findings using the Insights AI assistant | Click “Investigate” on a finding to explore its security implications interactively |
How to Access Insights
Users interact with these intelligence capabilities through the Insights page in the DryRun Security dashboard in two ways:
AI Assistant
The Insights page has an AI assistant chat interface. Users can interact with it to generate security reports, feature ship summaries, risk assessments, and more, all grounded in real DryRun Security findings data. Simply describe what you want (e.g., “Create a security summary for the features shipped this week”) and the assistant generates it from your actual scan data.
Example prompts:
- “What features shipped this sprint and what are their security implications?”
- “Show me the top vulnerability trends across my repos for the past quarter”
- “Which repos need the most attention right now?”
- “Generate an incident response summary for this vulnerability”
- “What AI coding tools are being used across our organization?”
- “Summarize the security posture of repo X”
Because DryRun Security continuously scans every pull request and repository, these responses are grounded in real findings from your codebase, not generic checklists. They pull from live data, so the answers reflect your current state.
Recurring Queries
Users can create recurring queries, which are scheduled questions that DryRun Security runs against findings data on a regular cadence. For example:
- A daily report on new critical findings across all repositories
- A weekly developer trend summary highlighting teams with the most new findings
- A monthly risk overview comparing finding rates period over period
- A sprint-aligned feature ship summary for release reviews
DryRun Security generates the reports automatically and delivers them on the configured schedule, keeping your team informed without manual effort.
MCP Integration
AppSec engineers and AI coding tools can also access the intelligence layer programmatically via DryRun Security's MCP integration. This enables AI coding assistants and agents to query findings, trends, and risk data directly from the development environment. See MCP Integration for setup instructions.