Finding Tuning with Feedback
Tune security findings and reduce false positives with feedback from developers and AppSec engineers.
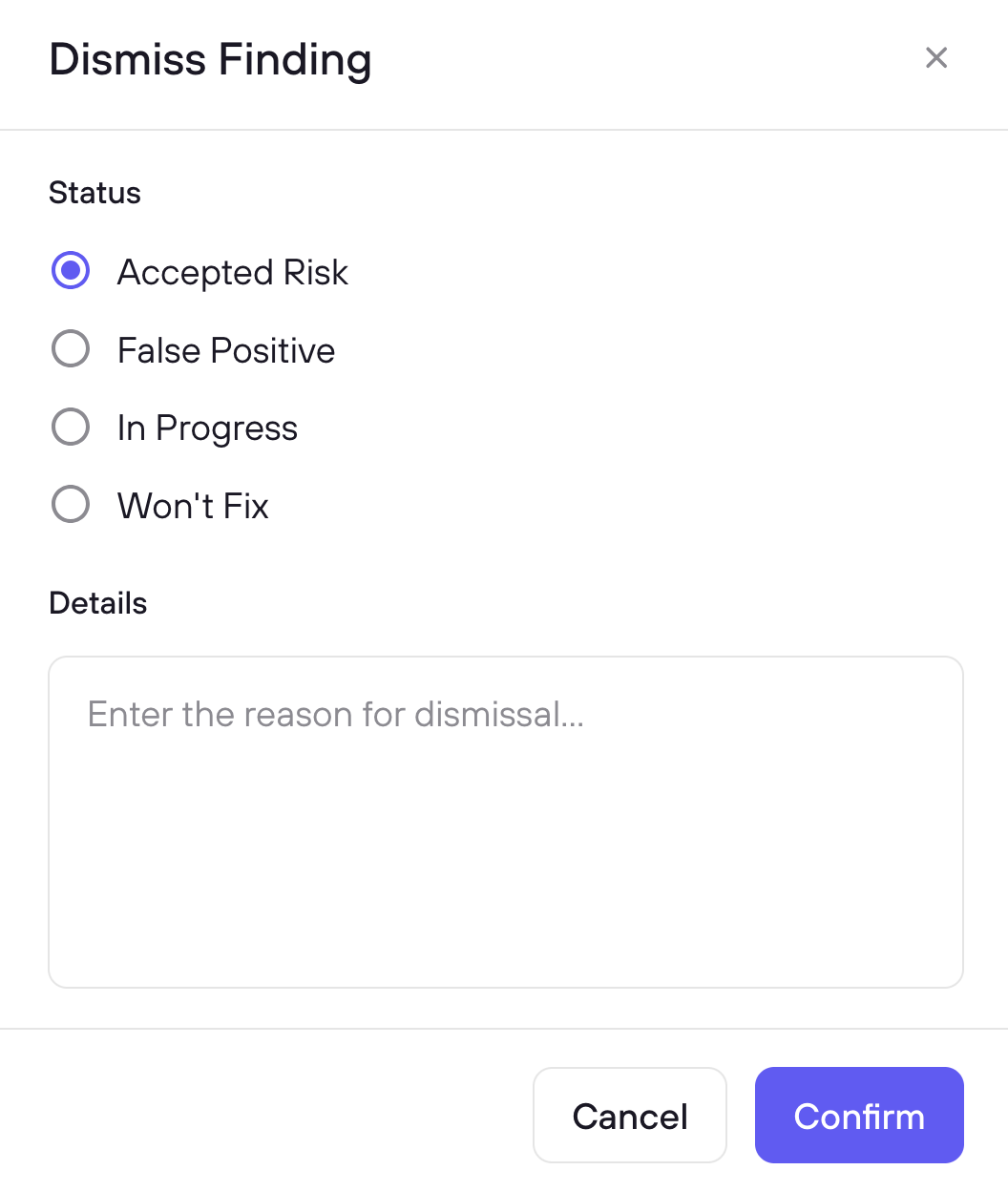
Developers and AppSec engineers can dismiss findings directly from the PR thread or the Risk Register dashboard. Every dismissal is logged for audit. Dismissals marked as False Positive or Won’t Fix / Nitpick also feed back into the model, improving scan accuracy over time.
Dismissal Statuses #
| Status | Description | Available From | LLM Learning |
|---|---|---|---|
| False Positive | The finding is not real or does not apply to the codebase. DryRun Security fingerprints the pattern and suppresses it in future scans. Context provided improves detection accuracy across similar patterns over time. | PR comment and Risk Register | Yes |
| Won’t Fix / Nitpick | The finding is valid but below the bar the team cares about, or the team has decided not to fix it. Feeds back into the model to reduce similar noise over time. | PR comment and Risk Register | Yes |
| Accepted Risk | The team knowingly accepts the risk and will not remediate it. Removed from the active view and SCM comment. Documented in the audit trail with the reason and who accepted it. | Risk Register | No |
| In Progress | A fix is planned but not yet applied. Removed from the active view and SCM comment. DryRun Security resolves it once the fix is applied. | Risk Register | No |
| Resolved | The finding has been addressed. Removed from the active view and SCM comment. | Risk Register | No |
False Positive and Won’t Fix / Nitpick dismissals feed into the Code Security Knowledge Graph, building a model of your codebase’s specific patterns and risk profile. Scan accuracy improves continuously as your team triages findings.
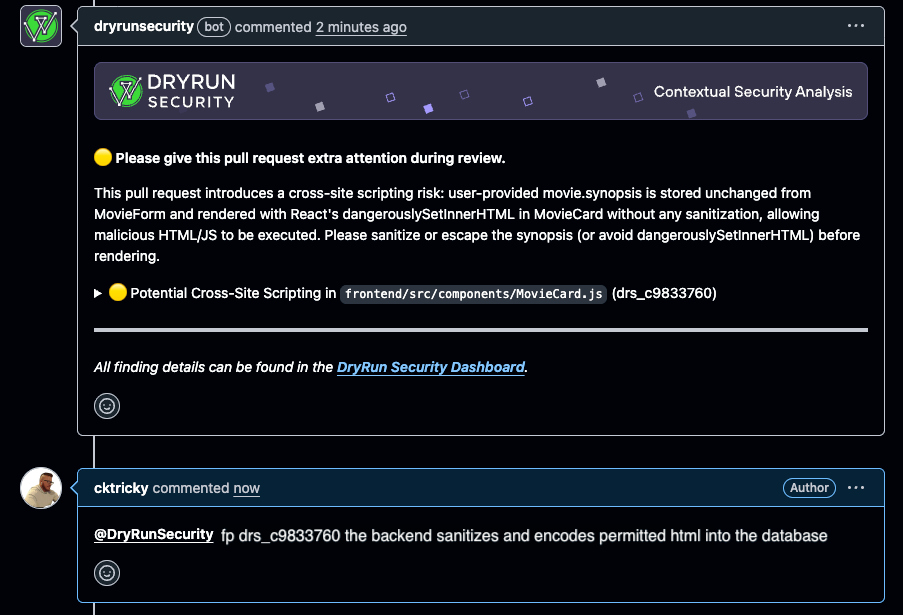
From the PR #
Developers can dismiss findings directly from the pull request thread without leaving their workflow. Dismissals sync to the Risk Register for AppSec review.
To mark a finding as a false positive:
@dryrunsecurity FP [issue ID] details why
To mark a finding as a nitpick:
@dryrunsecurity NIT [issue ID] details why
When a developer submits a dismissal, DryRun Security removes the finding from the active list, regenerates the PR summary comment, logs the decision for the audit trail, and feeds the signal back into the system.
If a finding is incorrectly blocking a merge via branch protection rules, developers can dismiss it directly in the PR thread. DryRun Security automatically removes the block without requiring AppSec intervention. The dismissal is logged so AppSec can review it afterward.
From the Risk Register #
AppSec engineers manage dismissals from the Risk Register, which provides a centralized view across all repositories and scan types. Select one or more findings using the checkboxes, then click Dismiss to choose a status and optionally add context.
From the Risk Register, AppSec teams can also:
- Override dismissals when a finding represents real risk that was incorrectly dismissed
- Monitor dismissal patterns across the organization to identify trends
- Use the audit trail to confirm all triage decisions are intentional and documented
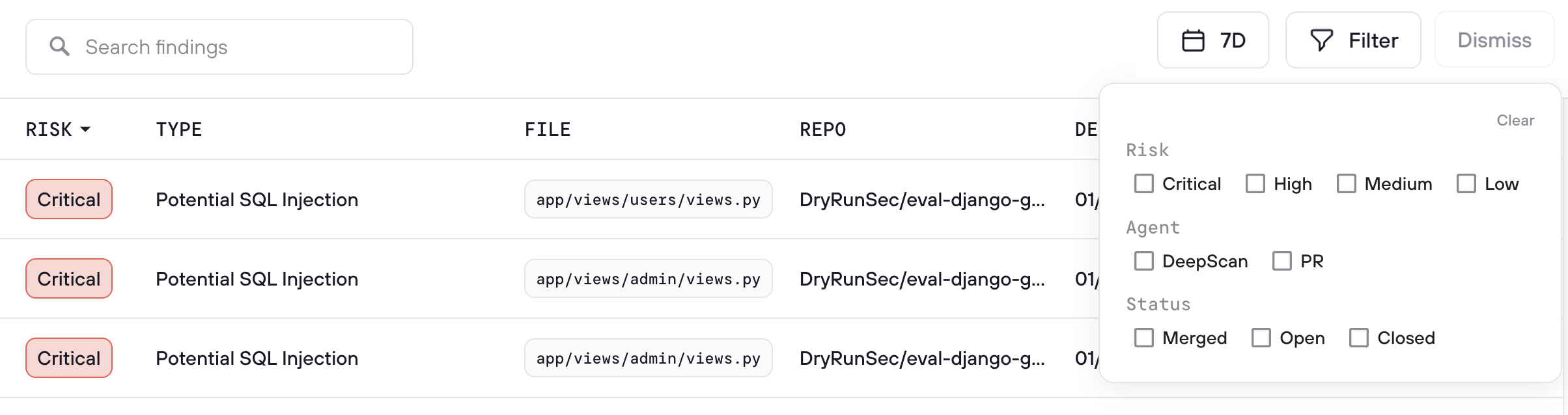
Dismissed Findings #
View dismissed findings in the Risk Register using the Dismissed filter. Each entry shows the dismissal status, reason, who dismissed it, and when. Use the Restore button to return a finding to the active queue if the dismissal needs to be revisited.
When a finding is valid but mitigating circumstances exist: Sometimes your team knows DryRun Security is right about a finding, but another layer of protection already addresses it. Rather than marking it as a false positive, the right resolution is to update your AGENTS.md with the context that explains why. This tells DryRun Security about the mitigating control so it does not raise the same class of issue again, without misrepresenting the finding as invalid. See Repository Context for details.